Shadow IT refers to unauthorized information technology resources within an organization. It can involve using unsanctioned applications, devices, or services, without the knowledge or approval of IT staff.
Shadow IT can pose several organizational risks, including data breaches, compliance issues, and decreased productivity. In some cases, shadow IT can even circumvent security controls or bypass corporate policies.
As such, organizations need to be aware of the risks associated with shadow IT and take steps to address them. One way to do this is by establishing clear guidelines for using information technology resources and consistently enforcing these rules.
Why Do Staff Use Shadow IT?

There are many reasons why staff can be tempted to use shadow IT. In some cases, they may be unaware of the risks associated with using unapproved software or devices. In other cases, they may believe that the benefits of using shadow IT outweigh the risks.
A recent study by Gartner found that the number one reason why staff use shadow IT is because they are not satisfied with the applications and devices authorized for use by the IT department.
Other reasons for using shadow IT can include the following:
Time Saving:
Staff may feel they can get their work done faster if they use unauthorized applications or devices.
Avoid Bureaucracy:
The process of getting approval to use specific information technology (IT) resources can be time-consuming and frustrating. In some cases, staff can bypass these procedures by using shadow IT.
Gain Access To New tools:
In some cases, staff may not have access to the tools they need to do their job because the IT department has not authorized them. As a result, they may turn to shadow IT to get the tools they need.
Unaware Staff:
Many employees are unaware of the potential harm they introduce to the corporate IT network. If confronted with the issue, they might ask, “what is shadow IT”?
Gain A Competitive Edge:
In some cases, staff may feel they can earn a competitive advantage by using unauthorized applications or devices.
Shadow IT Security Risks
Shadow IT can pose a severe security risk to businesses since these devices and applications may not be subject to the same rigorous security standards as those that the company officially sanctions.
Shadow IT can make it more difficult for businesses to comply with data privacy regulations. For example, suppose an employee uses a personal email account to send work-related messages. In that case, those messages may not be subject to the same level of security as they would be if they were sent using a company-approved email system.
Shadow IT can bypass security controls and introduce malware into the network. It can also create data silos that make it difficult to share information and track changes.
Shadow IT can introduce file sharing into the network, especially if users have weak or default credentials. The exposure to file sharing also brings on additional compliance concerns and the possibility of data leaks.
Shadow IT can make it more difficult for businesses to troubleshoot problems since they may not have visibility into the devices and applications used.

Every organization should be aware of the risks of shadow IT and take steps to mitigate them. By taking a proactive approach to managing shadow IT, organizations can protect themselves from these risks and ensure that their sensitive data remains secure.
The Solution To Shadow IT
So, what’s the solution to combating shadow IT? One solution is implementing zero trust network access (ZTNA). With ZTNA, all users and devices are treated as untrusted, whether inside or outside the corporate network.
Access is granted based on identity and context rather than location. This makes it more difficult for unauthorized users to access corporate data, as they need the correct credentials and access the data from a trusted device.
While ZTNA is not a silver bullet for shadow IT, it can help reduce the risk by eliminating the inherent trust assumption in traditional network security models. As enterprises increasingly move to a cloud-first approach, ZTNA will become an essential part of their cloud security strategy.
The Benefits of Shadow IT
Many organizations have embraced the BYOD (bring your own device) trend, leading to the rise of shadow IT. While shadow IT can pose security risks, there are also several potential benefits.
Shadow IT can give employees the flexibility to use the tools that they are most comfortable with, which can improve productivity. In addition, shadow IT can help to foster innovation by giving employees the freedom to experiment with new technology.
Of course, any decision to allow shadow IT should be made carefully, and organizations should put in place strict security controls to minimize the risks. Nevertheless, shadow IT can be a valuable asset for any organization when used appropriately.
What Are Shadow IT Applications?
Cloud-Based Applications:
Cloud-based applications are any application that is accessed via the internet. This includes SaaS applications (Software as a Service), such as Google G Suite, and IaaS (Infrastructure as a Service) applications, such as Amazon Web Services.
Shadow IT applications are often cloud-based because they are easy to set up and use without needing IT approval or assistance.
Cloud-Based Connected Apps:
Cloud services and apps are applications that connect to other cloud computing applications or services. An example would be a CRM (Customer Relationship Management) system that connects to an email service, such as Gmail, to import contact information automatically.
Some cloud-based services & connected apps can lack the proper cloud security and impose security gaps because they have the potential to introduce malicious code or file sharing into the network. For this reason, they should only be used if these cloud services come from a trusted source and have been approved by the organization.
Purchased Software:
Purchased shadow IT software is any software not provided by the business. This includes both off-the-shelf software and software that has been custom-developed.
Purchased software can pose security concerns because it may not be compatible with the organization’s security controls. In addition, it may not be subject to the same security testing and quality assurance procedures as in-house software.
For these reasons, any decision to use purchased shadow IT software should be made carefully and only after thoroughly evaluating the risks.
IT Department: Approval And Provisioning Process
The IT department approval and provisioning process are designed to ensure that all new IT equipment and programs meet the needs of the business. The first step is to submit a requisition to the IT department outlining the proposed purchase. The department head will review the petition and decide whether to approve the purchase. The department head will send a purchase order to the supplier if the purchase is agreed upon.
Once the equipment or programs has been delivered, they will be installed by the IT team and made available for use by employees. The entire process typically takes between two and four weeks. This is why staff decide to use shadow IT, because following proper procedures can take significant time, especially in organizations with compliance requirements.
How Your IT Department Can Overcome Shadow IT
The first step is to increase communication and collaboration with employees. When educating your employees about the risks of shadow IT, they won’t need to ask what is shadow IT? The IT department needs to understand why employees are using unauthorized applications and devices and work with them to find authorized solutions that meet their needs.
This will allow your IT department to apply the proper security standards to the shadow IT applications and devices as the other supported technologies. The next stage is having IT establish clear policies and procedures for approved applications and devices.
Third, IT needs to provide training on proper application and device use, as well as on security risks. By taking these steps, an IT department can overcome shadow IT and help keep their company data safe.
Tools For Managing Shadow IT
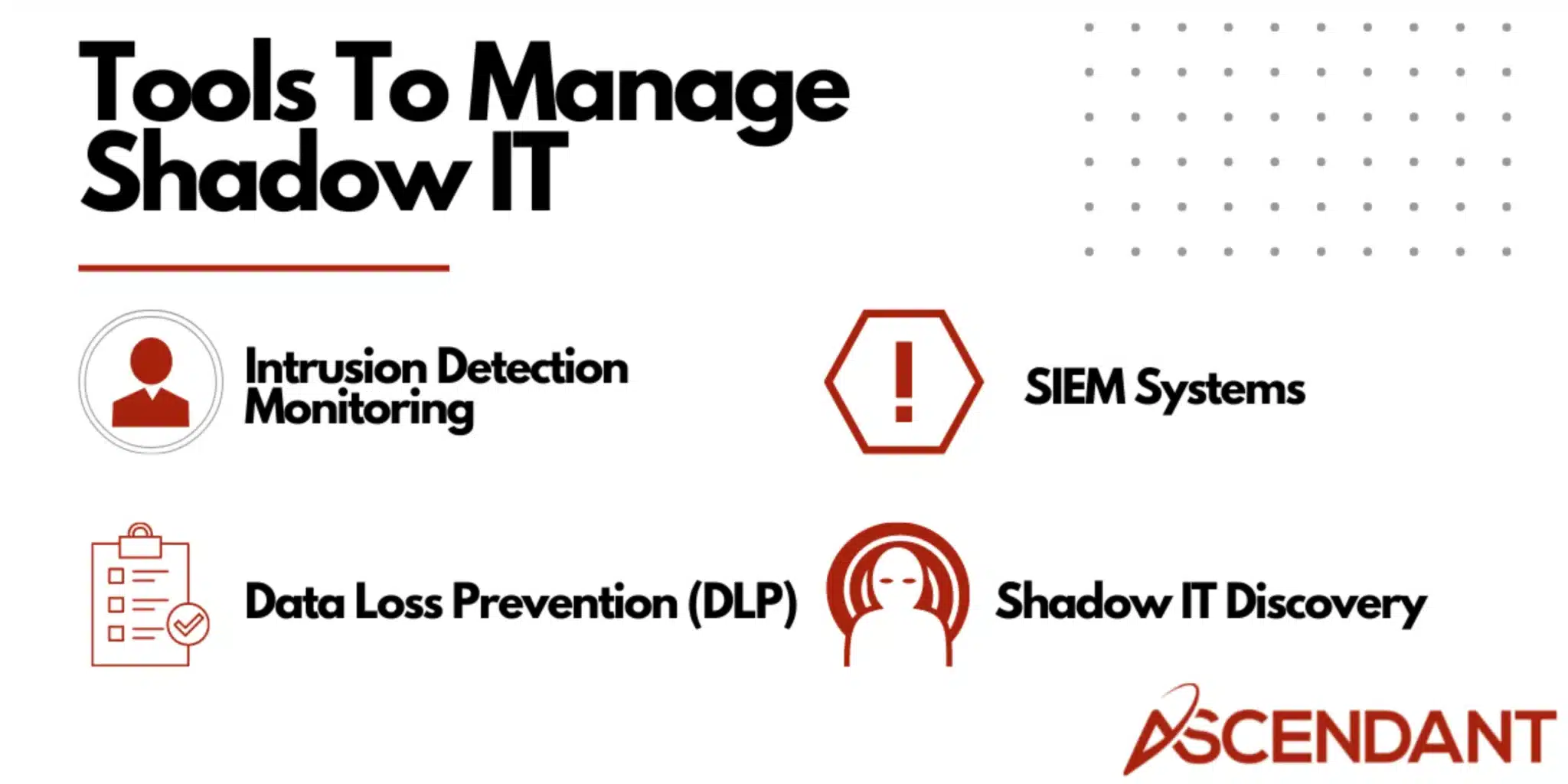
Several tools can help your IT security teams fight against shadow IT. These tools include:
Network monitoring and intrusion detection systems:
These systems can help identify unauthorized applications and devices on the network. In addition, they can detect malicious activity, such as data exfiltration, and alert the IT department.
Security information and event management (SIEM) systems:
SIEM systems collect data from various sources, including network security devices, firewalls, and IDS/IPS systems. This data is then analyzed to identify suspicious activity, such as attempts to access sensitive data or malware infections.
Data loss prevention (DLP) systems:
DLP systems can help protect sensitive data by identifying and blocking unauthorized access to it. DLP systems can also monitor email and file sharing activities to detect sensitive information sent outside the organization.
Shadow IT discovery tools:
These tools can scan an organization’s network to identify devices and applications not authorized by the IT department. Once unauthorized devices and applications are discovered, the IT department can take steps to block or remove them.
Manage Shadow IT With Ascendant
If your business is like most, you have a problem with shadow IT. Fortunately, there’s a solution: contact Ascendant Technologies. We specialize in managing shadow IT and can help to reduce the risks it poses to your business.
We’ll work with you to identify all unauthorized applications and devices within your company and then implement measures to control and monitor them. We’ll also provide training for your employees on using authorized applications and devices properly. By working with us, you can help to keep your business safe from the dangers of shadow IT. Contact us today to learn more.


