Phishing is a type of online fraud that occurs when criminals pose as legitimate businesses to trick unsuspecting victims into sharing sensitive information. The information phishers are after can vary, but it often includes login credentials, credit card numbers, and personal information such as addresses and Social Security numbers.
Phishing attacks can be highly sophisticated, becoming increasingly common as more people conduct their lives online. Businesses and individuals need to be aware of the dangers of phishing to protect themselves from this growing threat.
What Is A Phishing Email?
A phishing email is a type of email scam that attempts to trick the recipient into giving personal information, such as passwords or credit card numbers. The email may look like it’s from a legitimate source, such as a bank or online retailer, but it will usually have some kind of false or misleading claims. The attacker’s goal is to have you fill in your login credentials or banking information on their website.
The Types of Phishing Attacks
Phishing scams come in many different forms, but there are a few that are more common than others. Here are some of the most common types of phishing attacks:

Spear phishing:
Spear phishing targets specific individuals or organizations. This is typically a highly targeted attack. The attacker will send a personalized email that appears to come from a trusted source or legitimate organization, such as a bank, government agency, or an existing client.
The email will contain a link or attachment that, when clicked, will install malware or redirect the user to a fraudulent website. Spear phishing emails can cause significant damage to your organization by stealing sensitive data, financial information, or login credentials.
Business email compromise (BEC):
Business email compromise attacks will target businesses and usually involve spoofing the email address of a high-level executive. The attacker will then send an urgent request for payment or sensitive information. Because the email appears to come from a trusted source, many businesses have fallen victim to this type of attack.
Domain spoofing:
A domain spoofing attack involves creating an email address that is similar to a legitimate domain name. For example, if the legitimate domain name is paypal.com, the attacker might create an email address using the slightly different domain name paypa1.com. When users receive an email from the spoofed domain, they may not notice the difference and may click on a link or attachment that contains malware.
How are Phishing Attacks Delivered?
The phishing email scam:
This is the most common phishing scam. The scammers send out emails that look very official and often include a link to a fake website where the user is asked to enter their personal information.
The phishing phone scam:
This scam involves scammers calling people and pretending to be from a legitimate company or organization. They will usually try to get the person to give them their personal information or to purchase something from them. Phone phishing scams can also be known as voice phishing or vishing.
The phishing text scam:
This is similar to the phishing phone scam, but instead of calling people, the scammers will send a text message. They will often try to get the person to click on a link in the message, taking them to a fake website where they will be asked to enter their personal information. Phishing text scams can also be referred to as smishing or SMS phishing.
How to Avoid A Phishing Attack
Phishing attempts are becoming more common than ever. It’s important to avoid becoming a victim of these phishing scams. There are a few things you can do to avoid becoming a victim of a phishing attack, such as:
- Be wary of unexpected emails or texts, even if they look like they are coming from a trusted source. If you’re not expecting a message, it’s best to delete it without opening it.
- Be suspicious of emails that ask for personal information, especially if they include a link to a website. Don’t enter personal information unless you’re sure the website is legitimate.
- Don’t open attachments or click links in emails from people you don’t know.
- Implement an email filtering solution like Microsoft’s Advanced Threat Protection (ATP) to stop the attack before it lands in your inbox.
- If you think you may have been the victim of a phishing attack, change your passwords immediately. If you’ve entered debit/credit card details online, you should contact your bank or credit card company.
- Implement an employee cyber security training service for your staff. This will help your employees spot phishing attempts.
How To Identify Phishing Emails
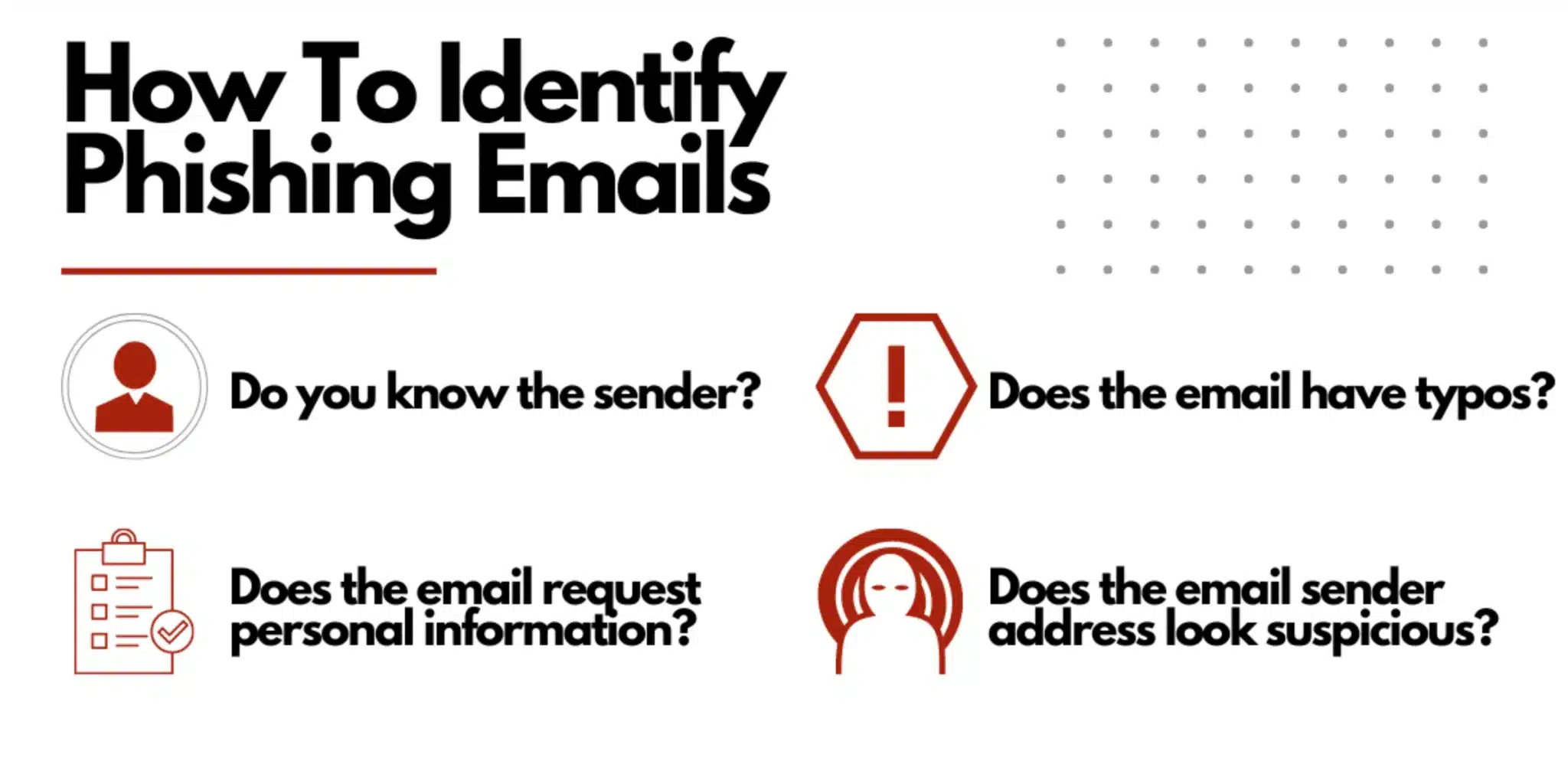
To protect yourself from falling victim to a phishing attack, it is important to be able to identify them. Here are some common signs that an email or other communication is a phishing attempt:
- You don’t know the sender, or the sender’s email address looks suspicious.
- The message includes typos or other grammatical errors.
- The message is urgent or includes threatening language.
- The message asks for personal information or financial details.
- The message includes a link to a website that you don’t recognize.
- The message asks you to click on a link or download an attachment.
- The message asks you to confirm or change information such as your email, account, etc.
Where To Report Phishing Emails?
Phishing attacks are a serious problem, and it’s important to know who to report them to help protect yourself and others. In the United States, the best place to report phishing attacks is the Internet Crime Complaint Center (IC3). The IC3 is a partnership between the FBI and the National White Collar Crime Center, allowing you to report internet-related crimes online.
That includes phishing attacks, as well as other types of fraud, such as identity theft and computer intrusion. When you report a phishing attack to the IC3, you’ll be asked to provide detailed information about the incident, including any evidence you have. This information will then be used to investigate the attack and bring the perpetrators to justice.
How To Identify A Phishing Website
Phishing websites are designed to look like a legitimate website that has been duplicated with fraudulent data entry forms. Some commonly phished websites would be banking websites or popular online services like Netflix, Apple, etc.
Here are some tips to spot malicious sites:
- Look for obvious mistakes in the web address. For example, malicious sites might have a web address similar to the real website, but with one small change.
- Check for spelling mistakes and poor grammar on the website. Phishing websites are often created by scammers who do not have a lot of experience in web design or English grammar.
- Hover your mouse over any links in the email or on the website, and check the text that displays in the bottom left corner of your browser window. If the link leads to a phishing website, the text will usually say “not secure” or “unsafe”.
- If you logged into a website and aren’t directed to the webpage you expected, you most likely filled out one of the scammer’s fraudulent data entry forms.
What To Do If You've Become A Victim Of A Phishing Scam
If you believe you have been the victim of a phishing scam, there are some important steps you should take to protect yourself.
First, change the password to the account that has been compromised. Be sure to use strong, unique passwords for all of your accounts. Using the same password for multiple accounts can grant hackers access to more than just the compromised account.
Next, check and monitor your credit report for any unusual activity. If you see anything suspicious, contact your financial institution immediately. Make sure there aren’t any lines of credit opened or new loans you don’t recognize. Hackers can cause significant identity theft damage with the right information from a phishing attack.
Finally, report the phishing attempt to the IC3 to fight against future phishing attacks and hold the hackers responsible for their crimes.
If You've Been A Victim of Phishing Scams, Contact Ascendant To Improve Your Cyber Security Posture!
If you’ve been the victim of a phishing attack, you’re not alone. Phishing attacks are becoming increasingly sophisticated and prevalent, targetting both individuals and businesses. If you’ve been the victim of a phishing attack, contact Ascendant Technologies today.
Our team of cyber security experts can help you to understand what happened and take steps to protect yourself in the future. Don’t suffer in silence – contact us today if you’ve been the victim of a phishing attack.


